Article
Do I Need SOC 2 for Enterprise Sales Before My First Enterprise Customer?
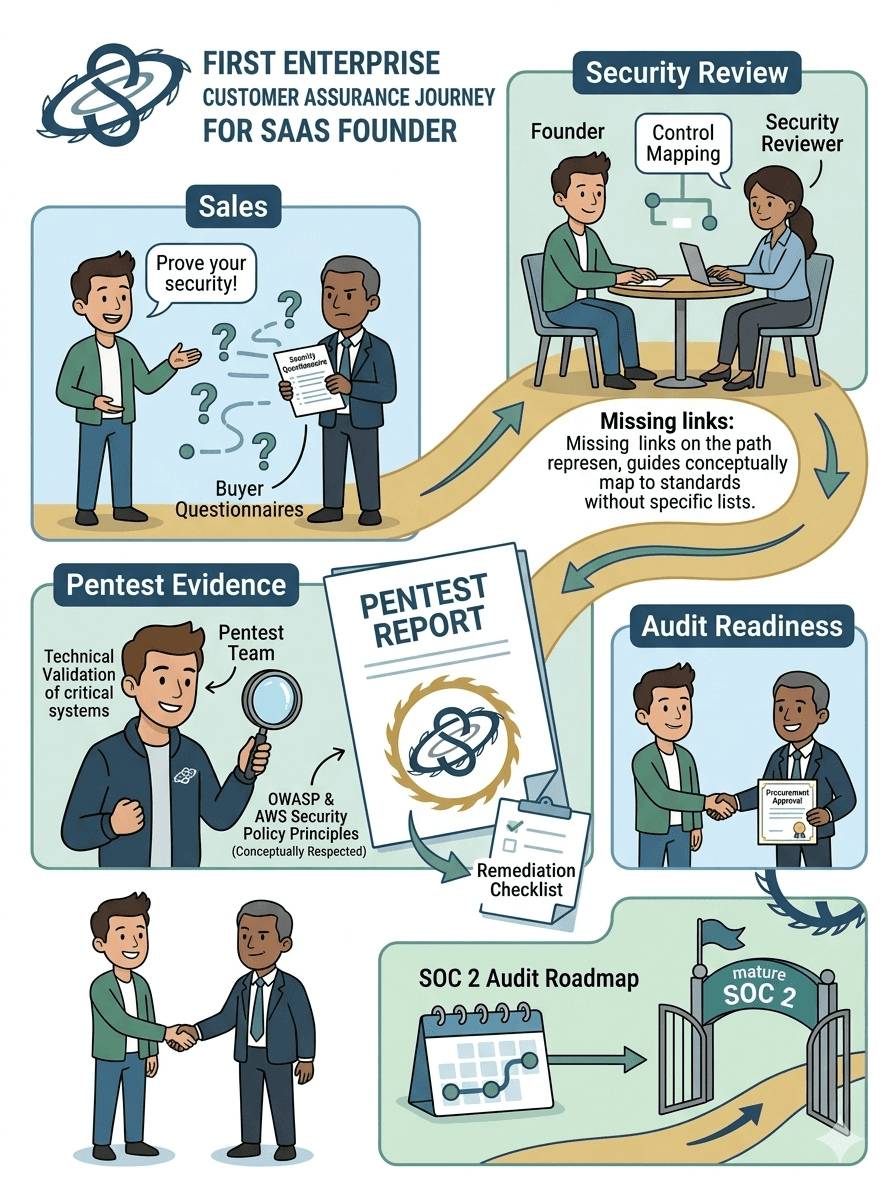
Enterprise buyers rarely need SOC 2 for the first conversation, but later procurement and security review often require stronger evidence. This article explains how to stage SOC 2, penetration testing, control narratives, and remediation proof for a first enterprise customer. It separates what SOC 2 proves from what offensive validation proves so founders avoid audit theater. It shows how to scope a focused pentest around the production application, API, tenant boundaries, identity flows, and cloud control plane.

If you are asking do I need SOC 2 for enterprise sales, the honest answer is usually no for the very first conversation and often yes for the later stages of procurement, security review, or renewal pressure. Enterprise buyers rarely care about the badge in isolation. They care about whether you can prove that customer data is handled inside a security program that survives scrutiny from procurement, security, legal, and sometimes their own auditors.
That distinction matters because many founders react to the first questionnaire by over-scoping the response. They buy a readiness platform, start writing policies, chase a Type II report before the deal is even qualified, and still fail the buyer review because they cannot answer technical questions about attack surface, tenant isolation, logging, remediation, or recent security testing. A cleaner approach is to treat the first enterprise deal as an evidence problem. SOC 2 is one evidence stream. A well-scoped penetration test is another. Architecture clarity, asset inventory, access control discipline, and remediation history matter just as much.
What SOC 2 actually proves
SOC 2 proves that your organization designed and, in a Type II engagement, operated controls relevant to the Trust Services Criteria for security, availability, processing integrity, confidentiality, or privacy. The AICPA frames SOC 2 as a report on controls at a service organization relevant to those criteria. That is useful to buyers because it reduces repetitive trust conversations. It does not prove that your application, APIs, cloud roles, admin paths, or business logic survived adversarial testing last week. A SOC 2 report is not a substitute for real offensive validation.
This is why founders get conflicting advice. Audit-led operators tell you to start SOC 2 early because enterprise deals stall without it. Offensive security practitioners tell you a clean pentest catches the technical failures that create real customer risk. Both are partly right. The mistake is turning them into substitutes. In practice, the buyer asking for a SOC 2 report is often saying something more concrete: show us independent evidence that your security controls are mature enough for us to trust your product with sensitive workflows and data.
When a deal needs stronger evidence
The best way to respond depends on where the deal actually sits. If the prospect is early and the champion is still proving internal value, a complete SOC 2 Type II report may be unnecessary. If legal, procurement, and security review are already active, the absence of any credible roadmap or evidence pack can kill momentum. The right question is not whether every startup needs SOC 2 before revenue. The right question is whether this specific sales motion now requires stronger third-party assurance than your team can currently provide.
Where pentest evidence fits
Where pentest evidence fits is simple: it is the technical proof that your externally reachable systems, critical identity paths, APIs, and privileged workflows were challenged like an attacker would challenge them. NIST SP 800-115 describes technical security testing as a way to identify vulnerabilities, validate them when appropriate, analyze findings, and support mitigation. OWASP WSTG then gives the practical structure for web and API testing, while the OWASP API Security Top 10 2023 highlights failure patterns such as broken object level authorization, broken authentication, and server-side request forgery that matter directly in modern SaaS environments.
What buyers expect in the evidence pack
When we scope a pentest for a startup in this position, we are not trying to generate a decorative PDF for a shared drive. We are testing the systems most likely to decide the buyer’s confidence. That usually means the production web application, core APIs, authentication and session flows, tenant boundary logic, admin functions, and the cloud configuration that supports them. If the app runs in AWS, the test also has to respect AWS security testing policy boundaries, including what is permitted on services like EC2, API Gateway, Lambda, RDS, CloudFront, and related infrastructure. That operational detail matters because a serious buyer can tell the difference between a pentest designed around the real environment and a recycled checklist.
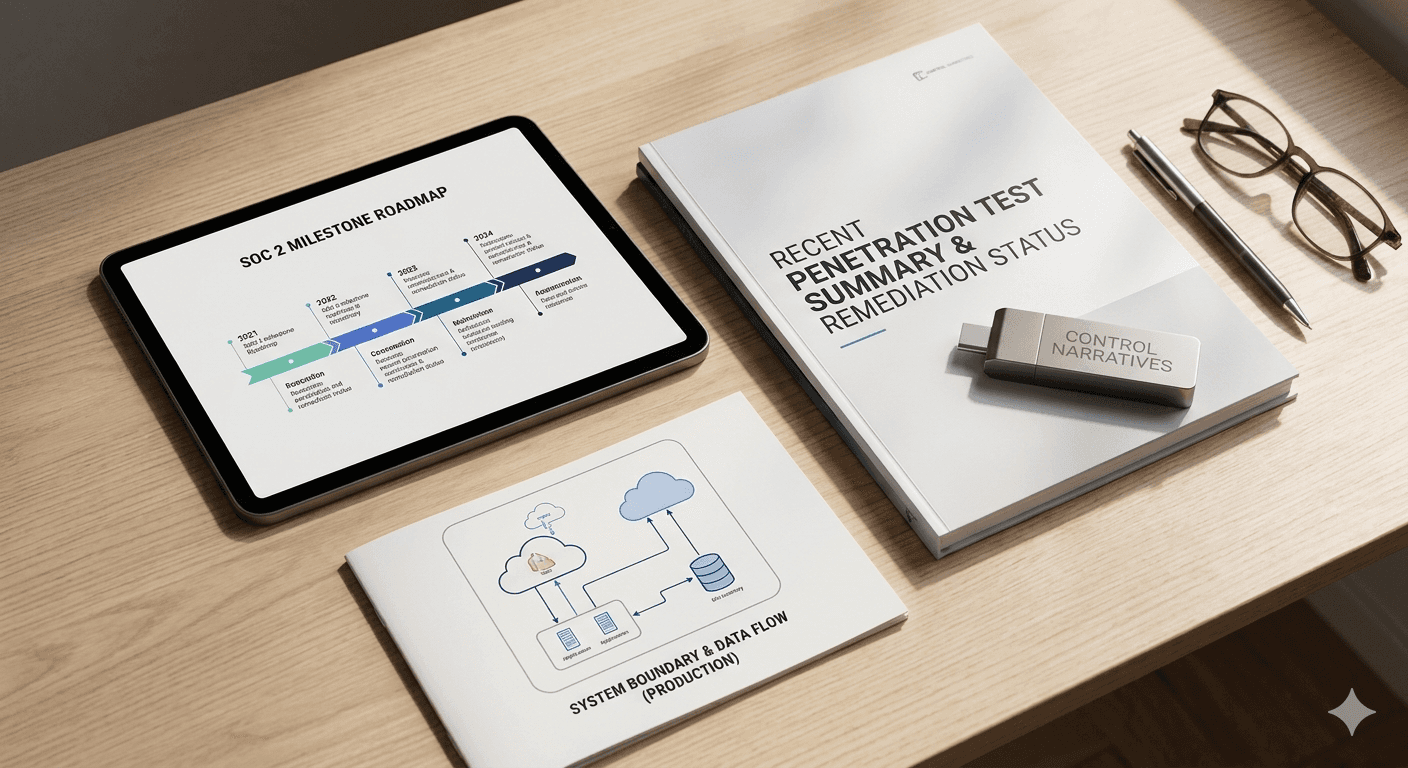
A useful evidence pack for the first enterprise deal usually contains four things: a clear system boundary that explains what data you store, where it flows, and what production components matter; a recent penetration test report or summary with remediation status; a concise control narrative covering access control, logging, vulnerability management, backups, change management, and incident response; and a realistic roadmap for the next assurance milestone, whether that is SOC 2 readiness, Type I, or Type II.
Buyers do not always need every artifact on day one, but they do need confidence that your team is not improvising under pressure.
This is where smaller teams can create leverage. A founder does not need an enterprise-sized compliance department to answer enterprise buyers well. They do need disciplined scoping. If your only exposed surface is a single SaaS application with a supporting API and a lean cloud footprint, then testing should start there. Spending on a bloated engagement that includes irrelevant internal segments, low-value staging assets, or speculative attack paths wastes money and often delays remediation on the systems that matter. Under-scoping is just as bad. If the buyer’s real concern is cross-tenant data exposure through API authorization flaws, a generic network-only test will not help.
What the pentest should validate
To make that concrete, consider the sort of issue a buyer actually worries about in a multi-tenant product:
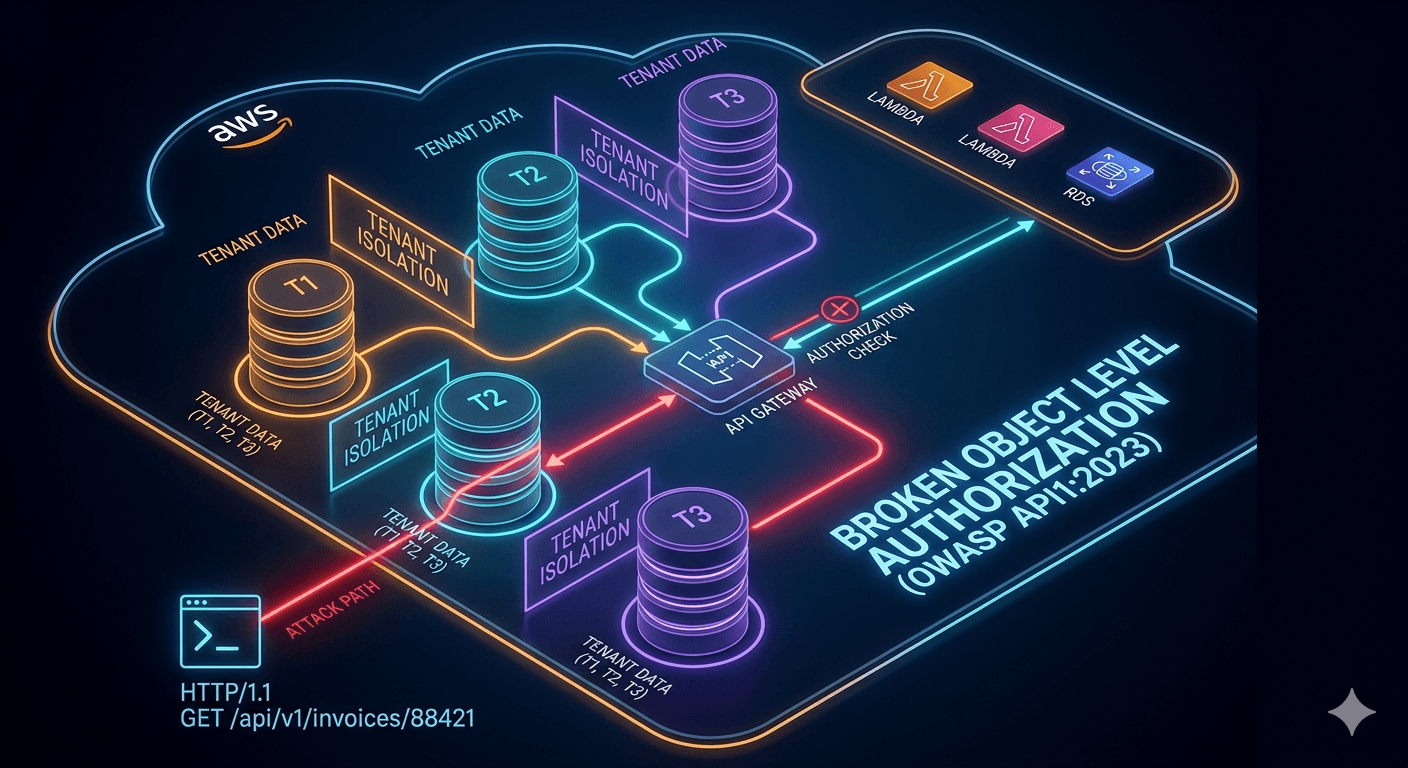
If changing that object identifier exposes another tenant’s invoice, the problem is not the absence of a policy. The problem is broken object level authorization. OWASP lists that as API1:2023 for a reason. A mature pentest will not stop at discovering the endpoint. It will validate authorization logic across roles, tenants, object references, admin functions, and related workflows. The report then needs to explain business impact in buyer language: cross-tenant data exposure, unauthorized access to customer records, or privileged workflow abuse. That is the kind of evidence procurement and security teams understand immediately.
The same logic applies to authentication, session security, and cloud control paths. A serious buyer wants to know whether the test validated session invalidation failures after logout, password reset, or token rotation; MFA and step-up authentication paths that can be bypassed through alternate flows; privileged cloud roles that exceed what the application design actually requires; administrative routes, support tooling, or tenant-management functions that can be enumerated or abused; and logging and monitoring paths that should detect the attack chain but do not.
Tools such as Burp Suite, ffuf, Nuclei, Semgrep, and cloud-native telemetry help, but the important thing is the methodology behind them. Buyers are not buying a scanner run. They are buying confidence that a competent team tested realistic paths with enough depth to say what was and was not validated.
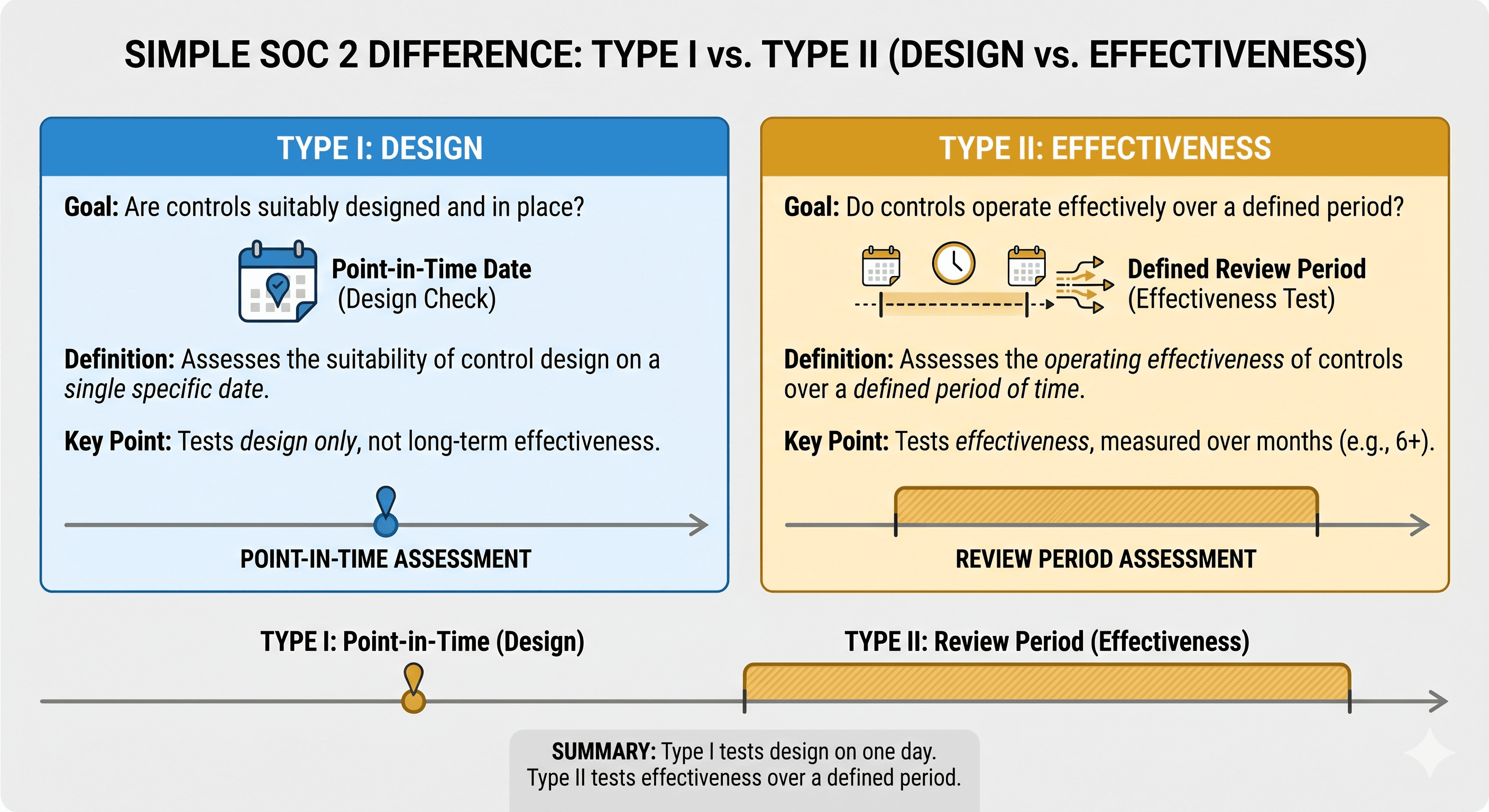
Timing Type I, Type II, and testing
That is why SOC 2 and pentesting should be timed together instead of argued as alternatives. If your first enterprise customer is six to twelve months out, the strongest path is often to begin the control program early, clean up identity and change-management gaps, and schedule testing once the production boundary is stable enough to produce evidence worth keeping. If the customer is in procurement now, you may need to compress the sequence. In that case, a focused penetration test plus a documented SOC 2 roadmap can be more persuasive than rushing into a premature audit that exposes weak operating evidence.
Type I and Type II decisions should be framed the same way. A Type I report tells the buyer that controls were suitably designed at a point in time. A Type II report carries more weight because it speaks to operating effectiveness over a review period. For a first enterprise deal, some buyers will accept a Type I plus strong technical evidence and a clear path to Type II. Others will not. The only useful answer is the one tied to the deal stage, buyer risk posture, and contract pressure. Founders lose time when they treat every prospect like the strictest possible buyer.
Avoid vendor threat
Vendor threat starts when the output is all assurance language and no technical specificity. Be careful with any pentest proposal that cannot tell you which assets are in scope, what test standard guides the work, how manual validation is separated from automated enumeration, how retesting is handled, or how findings will map back to business risk. The same caution applies to compliance programs that promise enterprise readiness without forcing the team to define the production boundary, control owners, logging expectations, and remediation cadence. Buyers can smell that kind of gap quickly once the questionnaire turns into a call.
A practical sequence
A practical path for a 15 to 80 person SaaS company usually looks like this: confirm what systems are actually in scope for customer data and privileged operations, clean up identity basics, logging coverage, and change control enough that an auditor or buyer can follow ownership, run a focused penetration test against the real production surface rather than an imaginary future architecture, fix the meaningful findings and retest them, and then decide whether the sales pipeline justifies going straight into SOC 2 readiness or into a formal Type I or Type II cycle.
That sequence protects time, budget, and engineering attention better than treating compliance as a race for the fastest badge.
Why Sudarshana fits this work
Sudarshana’s advantage in this kind of work is not audit threat. It is practitioner depth. When our OSCP, OSWE, OSEP, OSCP+, GCPN, CREST CRT/CPSA, eWPTXv2, and CEH Practical certified team scopes a compliance-led pentest, the goal is to show whether the systems that matter to the buyer actually hold up under realistic abuse. That means business logic, API authorization, identity workflows, cloud boundaries, and remediation evidence that can survive both engineering review and buyer scrutiny.
The founder question to ask
If you are preparing for your first enterprise customer, do not ask whether SOC 2 is a universal startup milestone. Ask what proof this buyer needs to trust your system, what proof you already have, and what proof you can produce fastest without faking maturity. That is the question that keeps deals moving and keeps your security program honest.
Need a penetration test scoped to your compliance requirements? Talk to our team at sudarshana.io/contact
#SOC2 #EnterpriseSecuritySales #PenetrationTesting #ComplianceSecurity #StartupSecurity #FounderAdvice #EnterpriseDeals #OWASP #APISecurityTesting #BrokenObjectLevelAuthorization #NIST #SecurityCompliance #SaaSecurity #CloudSecurity #TenantIsolation #BurpSuite #OffensiveSecurity #SecurityAudit #TypeITypeII #AICPA #SecurityEvidence #CybersecurityForStartups #PenTest #Cybersecurity #SecurityResearch
QUESTIONS
Schedule a call with the team that helped secure these companies.